Do we still need Active Directory groups in the age of Microsoft Teams?
I got an interesting question from one of my loyal followers the other day. They recently migrated to Microsoft 365 from the on-premises file server. Since they heavily used file shares and network drives with deep folder hierarchies, they had many Active Directory Groups created to control folder-level permissions within the file share. And since the client started to heavily rely on Microsoft Teams and Microsoft 365 groups in general, the question they had was whether they still needed to maintain any Active Directory (AD) Groups. Let me answer this for you.
Different types of Groups in Microsoft 365
First, to understand the difference between different groups, I suggest you read this article. A quick recap appears below.
Active Directory groups
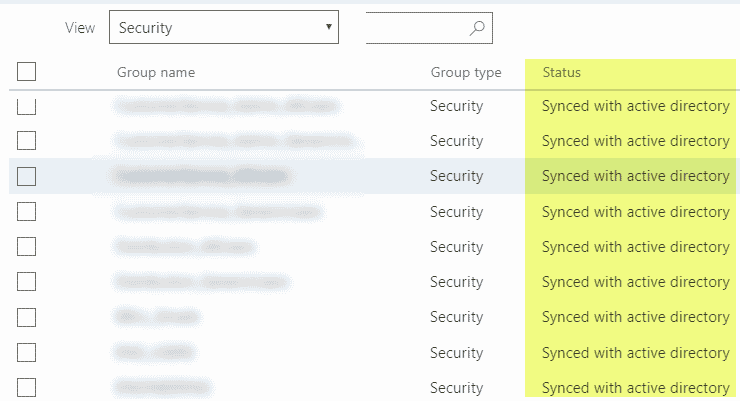
AD Group is just a “regular” security group that consists of members. It is created and maintained in Azure AD or can be synchronized from the on-premises AD.
Microsoft 365 Groups
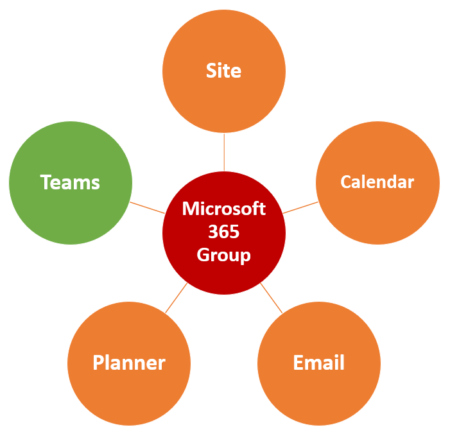
In contrast, Microsoft 365 Group is a security group “with benefits.” It is a relatively new concept introduced in 2016 that combines the security of a group with a membership that allows access to other applications within the Microsoft 365 eco-system.
Unlike the AD Group that can only be created by Admins behind the scenes, Microsoft 365 Group can be created by regular users. And it can be created from a vast list of places as well. The most common place to do these days – Microsoft Teams. When you create a new Team in Teams, it establishes a Microsoft 365 Group tied to the team, a SharePoint Site, plan in Planner, Outlook calendar, etc.
AD Groups vs. Microsoft 365 Groups
The original idea of AD Groups was that it allowed for IT Admins to easily create different security scenarios (rosters) and then use (and reuse) a single sec group to manage access to various assets (i.e., folders on a file server).
Microsoft 365 Group “democratizes” the process and allows “regular” Office 365/Team/SharePoint users (read all employees) to create their own Microsoft 365 Group. So in theory, this acts as a replacement for the old-fashioned AD groups.
It is essential to note that creating a Microsoft 365 Group creates other assets as well (i.e., Team in Team, SharePoint site, Group Calendar, etc.). And if one of the assets gets deleted, it takes down the other assets and the whole group.

Use cases for Active Directory groups in SharePoint and Teams
So do we still need AD Groups? The answer depends on the size of the organization as well as a few uses cases outlined below.
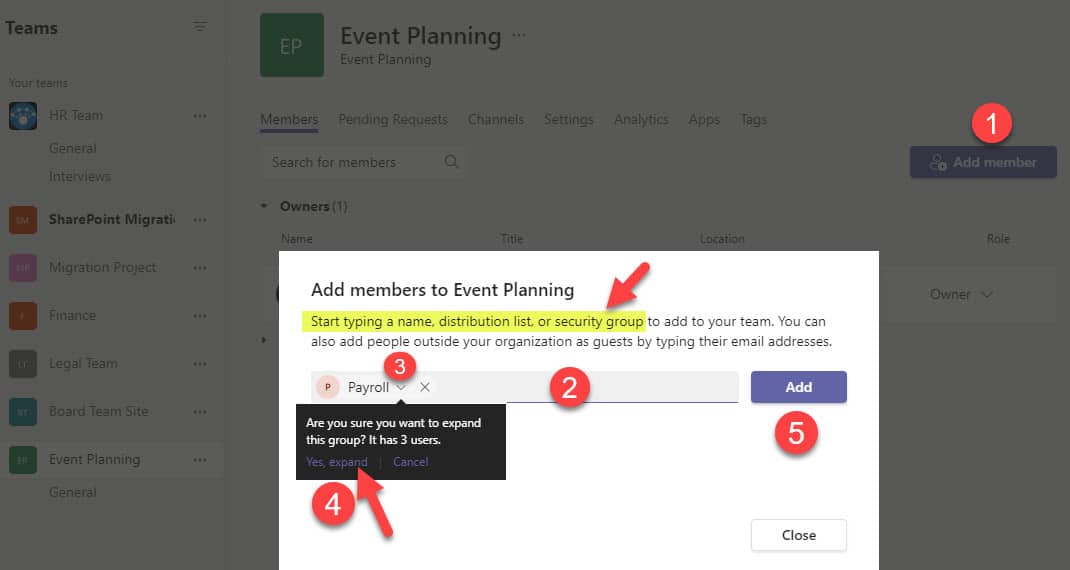
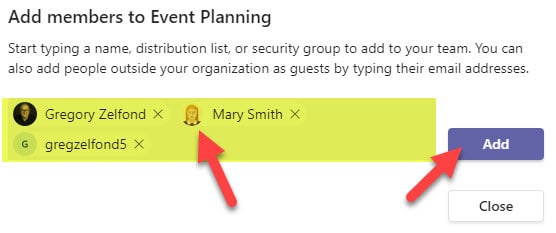
Use Case # 1. Manage membership of Microsoft Teams
If you are part of a large organization and need to add many members to the team, this might come in handy. However, it has some nuances. When you add a security group to a Microsoft Team, it just extracts the members from that AD group and adds them individually to the Team. If you then need to remove the group from the team, you would need to manually remove the added members one by one.
Use Case # 2. Manage Security of a SharePoint Site
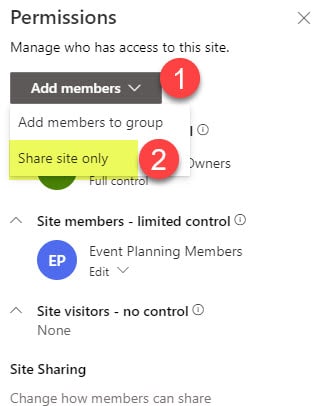
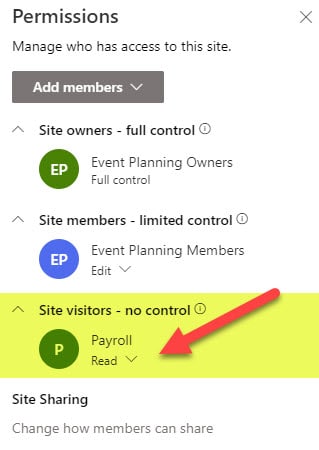
SharePoint site has a security/permissions setup of its own that can be managed independent of Teams/Microsoft Group membership. SharePoint security groups allow the nesting of Active Directory security groups, so you can manage site security using those if necessary.
Use Case # 3. Manage folder-level access
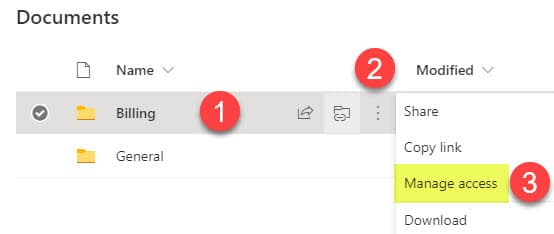
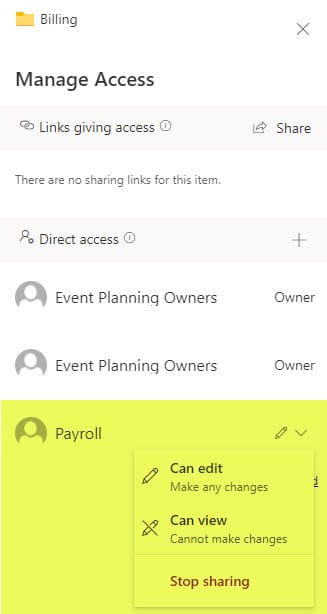
Where AD groups can become handy would be the folder-level permissions on a site. While I always advocate managing security at a site level, there are scenarios when you need to create unique security for libraries and folders. I describe how to create unique permissions for libraries and folders here.
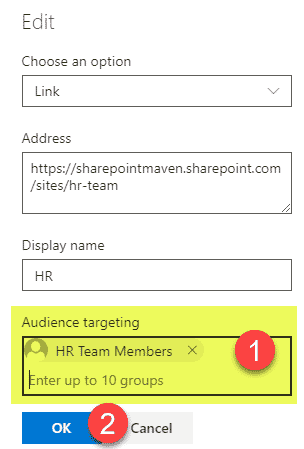
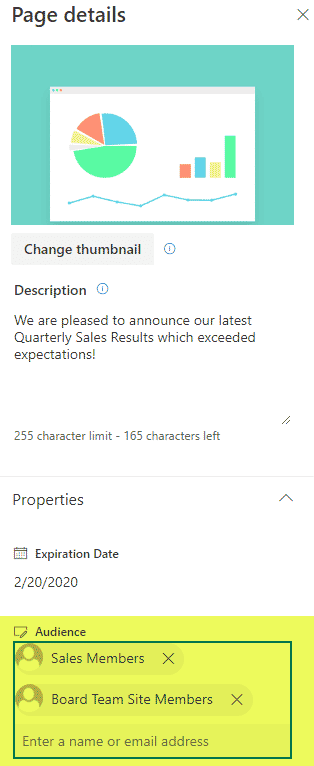
Use Case # 4. Manage the display of content and links via Audience Targeting
One other area where I think AD groups might still be handy is Audience Targeting. You can target different content in SharePoint to users (navigation links, news posts, quick links, documents, calendar events). I outlined most in this article. When you set up audience targeting, it asks you to add security groups (it does not allow you to add individual members). So once again, if you have dedicated rosters (AD Groups) of users maintained by IT – Mazel Tov, your job is much easier now!
Verdict
AD Groups can still be handy if you want to centrally control the security of certain groups and not be dependent on some Team owners to maintain the security of their Microsoft 365 Group (which is always fluid and can’t really be controlled).



